Three Frameworks, One Infrastructure Decision
Indian cloud compliance in 2026 is not a single framework. It is three overlapping sets of requirements, each with different origins, different enforcement mechanisms, and different specific obligations, that Indian organisations must satisfy simultaneously.
The CERT-In Mandatory Directions of April 2022 are operational security requirements focused on incident reporting, log retention, and system security practices. They apply to all service providers, intermediaries, data centres, and government organisations operating in India. The CERT-In Comprehensive Cybersecurity Audit Policy Guidelines, issued in July 2025 and effective from 25 July 2025, have added a further layer: mandatory annual third-party audits for all public and private organisations, conducted exclusively by CERT-In empanelled firms, with board-level accountability required for all risk treatment decisions.
The Digital Personal Data Protection Act 2023, combined with the DPDP Rules 2025 notified on 13 November 2025, represents India's most significant privacy legislation. The Rules bring the Act into operational force in a phased manner. The Data Protection Board of India (DPBI) was established on 13 November 2025 and is now operational. Full enforcement, including financial penalties of up to INR 250 crore (~$26M) per violation, is on a documented and accelerating trajectory through 2026 and into 2027. All USD equivalents in this article use a conversion rate of Rs.94.91 per dollar as of May 2026.
The MeitY Cloud Empanelment Framework, the Ministry of Electronics and IT's programme for evaluating cloud providers for government use, remains the procurement reference for government agencies, PSUs, nationalised banks, and financial institutions under the GI Cloud / MeghRaj initiative. In November 2025, MeitY also released India's Artificial Intelligence Governance Guidelines, extending its regulatory footprint into AI-driven workloads that depend on the same cloud storage infrastructure covered by the other two frameworks.
The challenge for compliance teams is that these three frameworks ask related but different questions about the same infrastructure. CERT-In asks where your logs are, how quickly you can retrieve them, and whether your annual audit has been completed by an empanelled firm. The DPDP Act asks where your personal data is, under whose legal jurisdiction it falls, and whether you can demonstrate reasonable security safeguards to an operational enforcement board. MeitY asks whether your cloud provider has been evaluated against government security standards. A cloud infrastructure decision that satisfies one framework may not satisfy the others.
CERT-In Mandatory Directions: What They Require in 2026
The April 2022 CERT-In Mandatory Directions remain the operational foundation. Their core obligations are unchanged: 180-day log retention within Indian jurisdiction, six-hour incident reporting across 20 categories of cybersecurity incidents, NTP synchronisation to NIC or NPL servers, and data localisation for log storage.
What changed materially in 2025 is the audit obligation. The CERT-In Comprehensive Cybersecurity Audit Policy Guidelines, issued in July 2025, make annual cybersecurity audits mandatory for both public and private organisations. These audits must be conducted by CERT-In empanelled auditors, not by internal security teams. Scope must cover the entire digital estate: IT systems, web and mobile applications, APIs, cloud services, databases, and operational technology where applicable. Auditors are required to map controls against ISO 27001, NIST CSF, CIS Benchmarks, and OWASP, and to assess vulnerabilities in terms of real-world exploitability rather than theoretical risk.
The guidelines also introduce board-level accountability that compliance teams should note. Risk treatment decisions and exceptions must be authorised by the head of the organisation, which means cybersecurity risk is now formally a governance matter, not a delegatable IT function. In 2025, CERT-In empanelled 231 cybersecurity audit organisations, significantly expanding the capacity available to Indian enterprises seeking compliant auditors.
A second notable change is that audits are now required before any major infrastructure or application change, in addition to the annual cycle. An organisation migrating to a new cloud provider, or expanding its storage architecture, now triggers a pre-change audit obligation. Organisations that had treated their annual audit as a year-end formality need to integrate audit readiness into their change management process.
The practical implication for log storage remains the same as under the 2022 Directions: logs must be within Indian jurisdiction held by an Indian-entity cloud provider. A cloud provider with a Mumbai data centre but an American legal entity does not satisfy this requirement. IBEE includes audit logging with 180-day retention within Indian jurisdiction as a standard feature, which is one reason we have seen engineering teams building audit-ready stacks select it as the default log storage destination without additional configuration.
DPDP Act: What It Requires in 2026
The Digital Personal Data Protection Act 2023, now activated by the DPDP Rules 2025 notified on 13 November 2025, is no longer pending legislation. The Data Protection Board of India is constituted and operational. Penalties are not future-state numbers. They are the current enforcement structure.
The phased implementation timeline matters for planning. Phase 1, effective 13 November 2025, established the DPBI and its processes, including a fully digital complaints and adjudication portal. Phase 2, effective 13 November 2026, activates the Consent Manager ecosystem and intensifies oversight of Significant Data Fiduciaries, including their data localisation obligations and the requirement to appoint a Data Protection Officer resident in India. Phase 3, covering the remaining substantive obligations for all data fiduciaries, follows through mid-2027. Organisations likely to be designated Significant Data Fiduciaries, broadly those with more than 50 lakh users or INR 250 crore in annual revenue, should treat November 2026 as their primary planning horizon.
The penalty structure merits explicit documentation within compliance teams. Failure to implement reasonable security safeguards to prevent a personal data breach carries a penalty of up to INR 250 crore (~$26M) per violation. Failure to notify the DPBI and affected individuals of a breach carries up to INR 200 crore (~$21M). General violations of the Act or its Rules carry up to INR 50 crore (~$5M). A single data breach can theoretically attract both the security safeguard penalty and the notification penalty simultaneously, since each violation is assessed independently by the DPBI. The business case for compliant infrastructure has rarely been more straightforward to calculate.
For cloud infrastructure decisions, the most immediately consequential obligations relate to data fiduciary accountability, reasonable security safeguards, and breach notification readiness. Data fiduciary accountability means organisations are answerable to the DPBI for how personal data of Indian citizens is stored and protected, including how their cloud infrastructure handles it. Reasonable security safeguards, interpreted in the context of ISO 27001 and the CERT-In audit framework, encompass encryption at rest and in transit, access controls, audit logging, and incident response capability. Breach notification within 72 hours requires the same logging and monitoring infrastructure that CERT-In mandates separately.
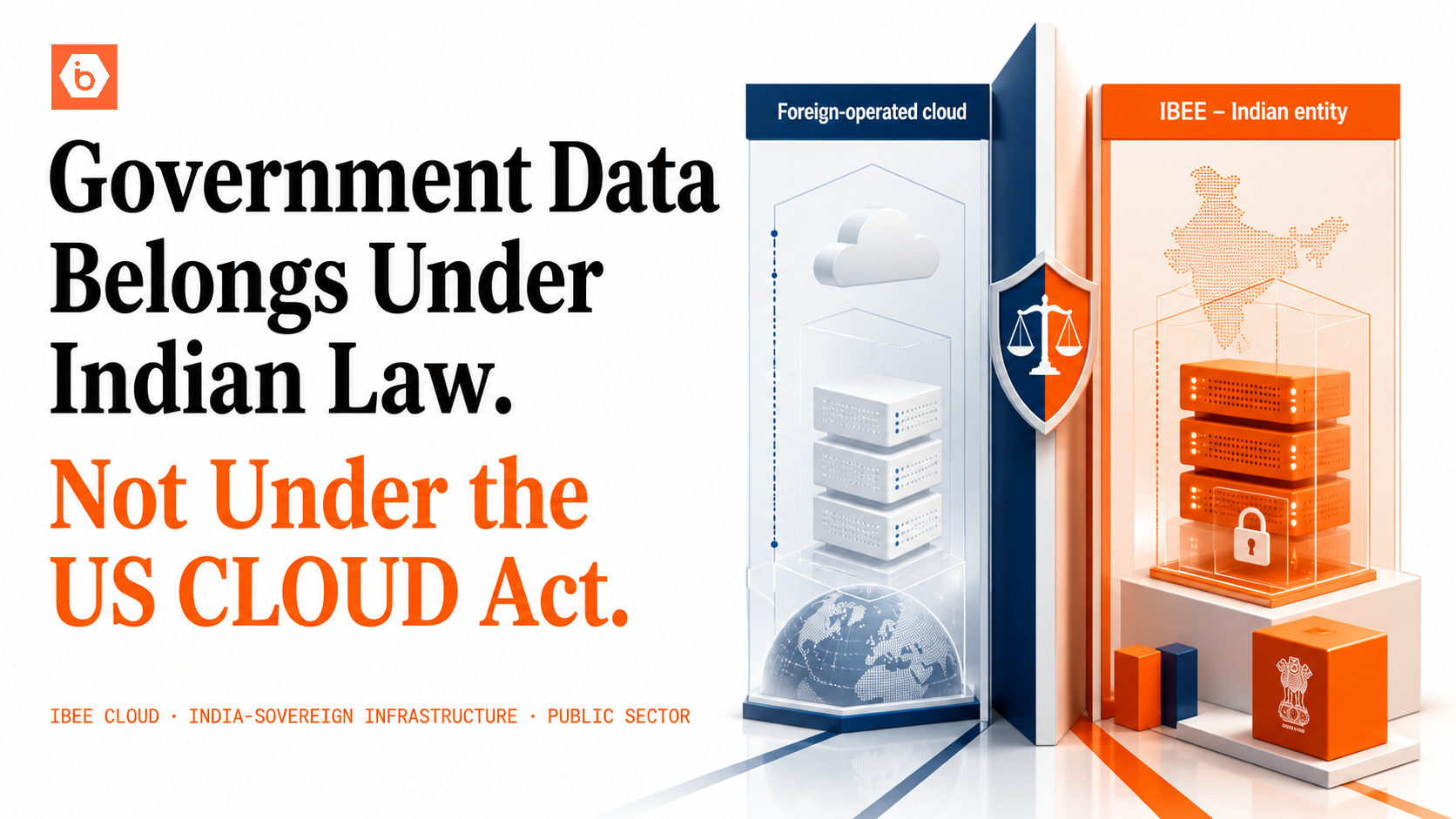
The jurisdictional question is central to DPDP compliance, and it is the question that creates the sharpest distinction between India-sovereign storage and foreign-operated cloud. We have spoken with compliance officers at regulated financial entities who cleared every other DPDP readiness checkpoint only to stall on this question, because their primary cloud storage remained governed by a foreign legal entity subject to US federal law.
If personal data of Indian citizens is stored on a foreign-operated platform, the data fiduciary's accountability may be complicated by the foreign operator's own legal obligations to non-Indian authorities. AWS and GCP maintain data centres in India. Their parent entities are American, and US authorities can compel access to data stored anywhere in the world under the CLOUD Act. IBEE is an Indian entity. Data stored on IBEE is governed by Indian law, stored within India, and accessible to Indian authorities through Indian legal processes. That complete jurisdictional chain is the infrastructure-level answer to the DPDP accountability question.
MeitY Empanelment: What It Signals in 2026
MeitY's empanelment framework evaluates cloud providers against security, reliability, and data governance standards established under the MeghRaj / GI Cloud initiative. Empanelled providers must comply with data localisation requirements and maintain ISO 27001:2017, ISO 27017:2015, ISO 27018:2019, and ISO 20000-1:2018 certifications, with annual surveillance audits conducted by the STQC Directorate.
The important 2026 addition from MeitY is the India Artificial Intelligence Governance Guidelines, released November 2025. These guidelines extend governance expectations into AI-driven workloads: the AI Governance Group, the Technology and Policy Expert Committee, and the proposed AI Safety Institute together form the oversight architecture for AI systems deployed on cloud infrastructure. For organisations running AI pipelines on Indian cloud, MeitY alignment now encompasses not just storage and compute governance but the data provenance and sovereignty requirements of AI training datasets and inference workloads. This is relevant to any organisation storing datasets in object storage for model training or fine-tuning, because the data residency requirements of the AI Governance Guidelines align directly with those of CERT-In and the DPDP Act.
For govtech companies, regulated financial entities, and IT system integrators working with government clients, MeitY alignment remains a practical procurement requirement and, since the AI Governance Guidelines, an increasingly active one.
The Intersection: Where the Three Frameworks Converge in 2026
The practical convergence point of all three frameworks is data residency under Indian jurisdiction, and in 2026 that convergence point has an enforcement body behind it.
CERT-In requires logs to be within Indian jurisdiction and mandates annual empanelled audits that will scrutinise where those logs are stored. The DPDP Act creates financial accountability, up to INR 250 crore per violation, for personal data that is not adequately protected under Indian law. MeitY's empanelment framework requires Indian-entity providers for sensitive workloads. A single infrastructure decision, choosing India-sovereign cloud storage, addresses the data residency requirement across all three frameworks simultaneously.
Physical location in India is not sufficient. The cloud provider must be an Indian entity, governed by Indian law, with data governance that runs entirely through Indian legal institutions. IBEE is an Indian entity. Its infrastructure is Tier 4 certified with a 99.995% uptime SLA. AES-256 encryption at rest and TLS 1.3 in transit are default-on, not optional add-ons. The jurisdictional chain is complete and documentable.
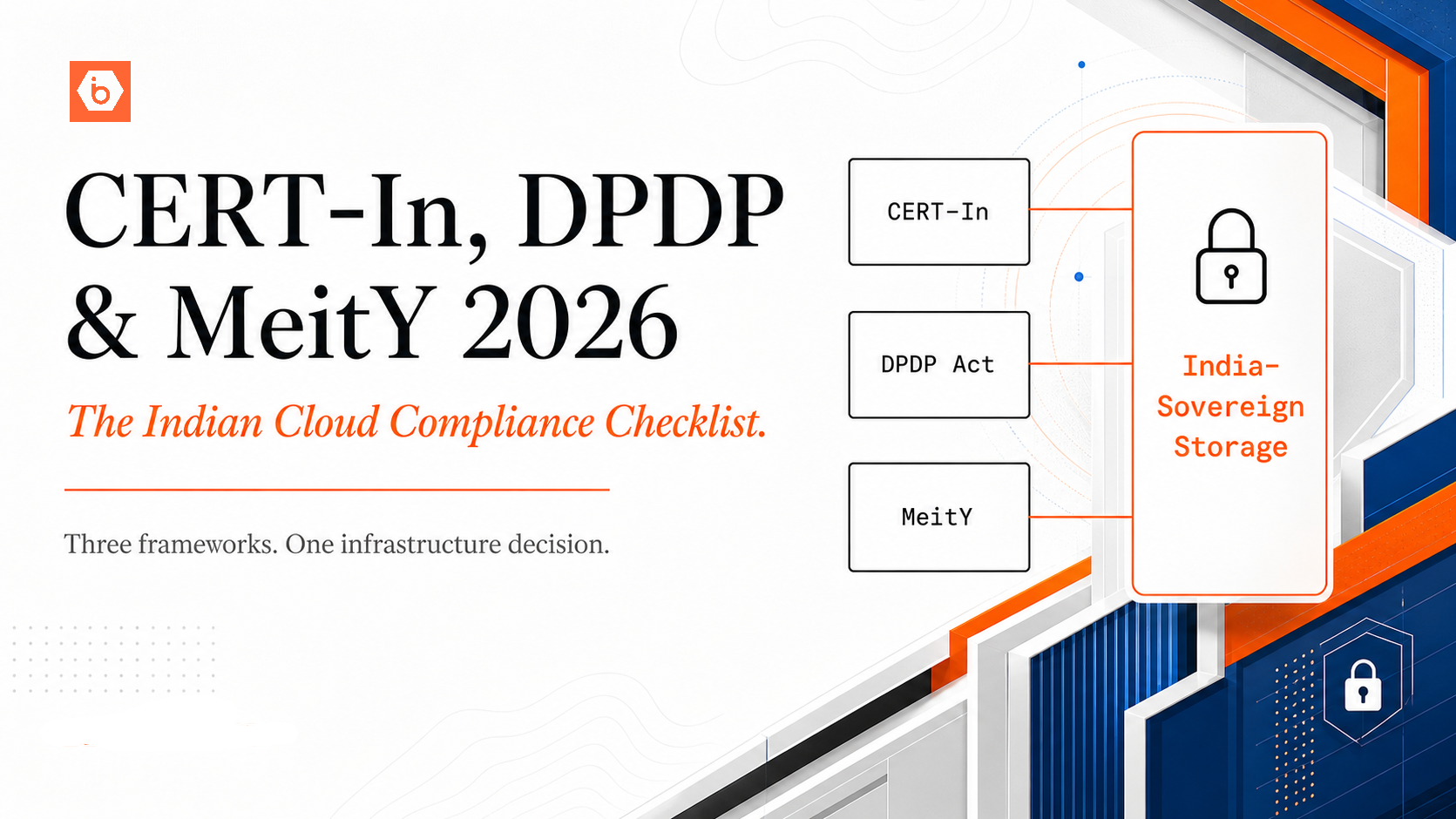
The table below shows how CERT-In, the DPDP Act with its 2025 Rules, and MeitY Empanelment map against the key compliance dimensions for 2026 planning.
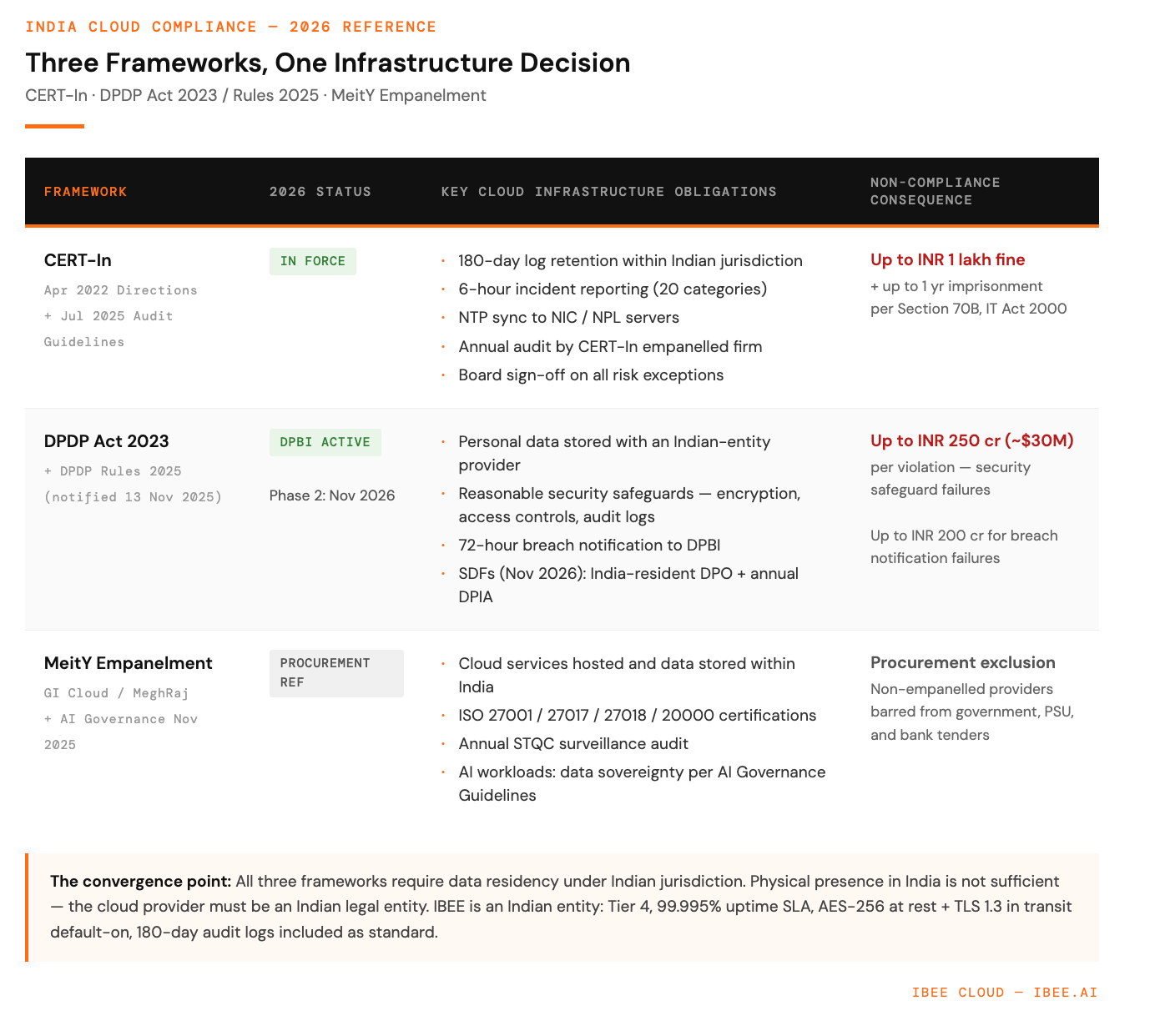
CERT-In, DPDP Act 2023 / Rules 2025, and MeitY Empanelment
The 2026 Compliance Checklist
The diagram below shows how the three frameworks map onto a single India-sovereign storage architecture, illustrating the data residency and reporting chain that all three collectively require.
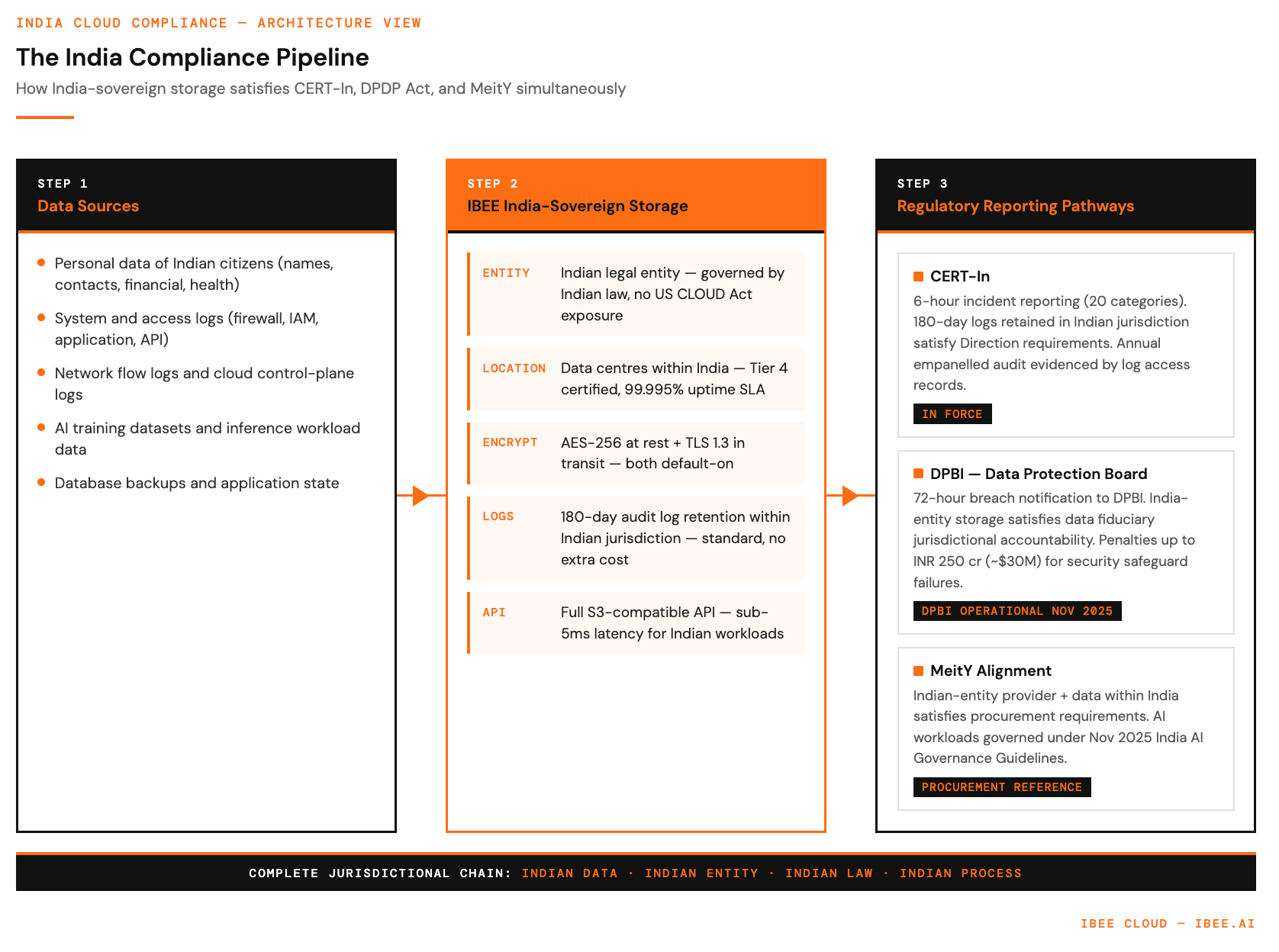
The India compliance pipeline