For CTOs, technology heads, and compliance officers at fintech startups, banks, NBFCs, insurance companies, payment aggregators, and wealth management platforms in India.
The Compliance Time Bomb Inside Most Indian Fintech Stacks
A payment aggregator in Mumbai gets a routine audit query from their banking partner. The question is straightforward: confirm that all transaction data, KYC records, and payment logs are stored exclusively within Indian legal jurisdiction and cannot be accessed by any foreign authority without Indian court authorisation.
Their engineering team pulls up the infrastructure documentation. AWS ap-south-1. Mumbai region. Physically in India.
That answer satisfies nobody on the legal side. Because "Mumbai region" on an AWS server is not the same as "Indian legal jurisdiction." Amazon Web Services is a US-headquartered company. Under the US CLOUD Act, American federal authorities can compel AWS to disclose customer data, including Indian financial records, regardless of which country that data physically sits in. No Indian court order required.
The audit drags on for three months. The banking partnership is delayed. The cost of that delay, in lost revenue and legal fees, runs into lakhs.
This is the compliance reality that Indian fintech companies, NBFCs, insurance platforms, and wealth management firms are walking into when they default to hyperscaler infrastructure, often without realising it until the audit is already in progress.
Most compliance teams we speak to discover this gap at the exact moment they can least afford it: during a regulatory inspection, during a banking partner onboarding, or during a Series B due diligence process where an investor's legal team asks the jurisdiction question. The infrastructure decision was made two years earlier by an engineer who had never heard of the CLOUD Act.
A Real Scenario: The NBFC That Failed Its RBI Audit Prep
Take an NBFC with Rs.500 crore AUM running a digital lending platform, processing 15,000 applications every month. Solid team, growing business. Cloud stack on a major hyperscaler's India region, storing loan documents, credit bureau data, repayment records, and KYC files.
As part of an RBI inspection preparation, their compliance team is asked to produce three things: written documentation confirming that all borrower financial data is stored and processed under Indian law with no cross-border data access possible without Indian legal process; evidence that system and access logs are retained for 180 days within Indian jurisdiction per CERT-In's April 2022 mandatory directions; and confirmation that data replication or backup does not occur outside India without explicit approval.
Their hyperscaler can document physical location. It cannot document Indian legal jurisdiction. The US CLOUD Act exposure is structural — it cannot be configured away. The CERT-In log retention is technically achievable but requires significant additional configuration and additional cost through the hyperscaler's audit logging add-ons.
Their compliance team spends four months and Rs.18 lakh in consulting fees attempting to produce documentation that their cloud provider structurally cannot support.
RBI, SEBI, IRDAI, and CERT-In are not softening their data localisation expectations. Every quarter, the documentation bar for regulated financial entities gets higher. The fintech companies building on India-sovereign infrastructure now are the ones that will clear audits cleanly. The rest are building compliance debt that compounds.
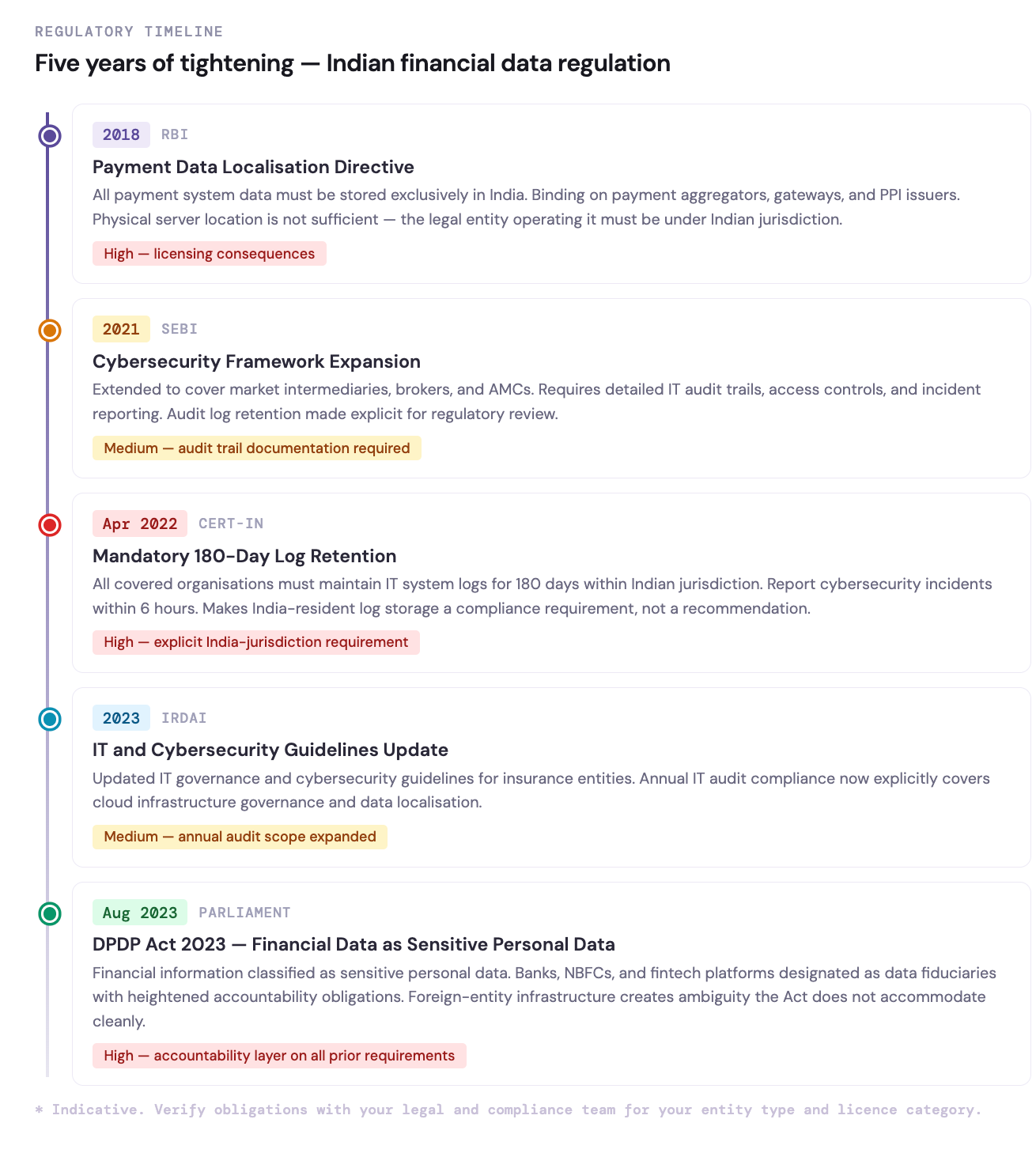
Each directive added a new documentation requirement that hyperscaler infrastructure cannot satisfy cleanly.
Why Hyperscaler Infrastructure Creates Structural Risk for Indian Financial Services
The problems Indian BFSI companies face on hyperscaler cloud are not configuration problems. They are structural — built into the legal and business architecture of global cloud providers.
The RBI Data Localisation Mandate
The Reserve Bank of India has required since 2018 that all data related to payment systems — transaction records, end-to-end payment details, customer financial data — must be stored exclusively in India. This is not a recommendation. It is a binding directive, and non-compliance carries licensing consequences for payment aggregators, payment gateways, and prepaid instrument issuers.
Storing this data on AWS or GCP's India region does not satisfy the RBI mandate if the data can be accessed by the cloud provider's foreign parent under US law. The physical location of a server is not the same as the legal jurisdiction governing data access. Most fintech legal teams learn this distinction during their first serious regulatory review.
The SEBI and IRDAI Audit Trail Problem
SEBI's cybersecurity framework and IRDAI's IT guidelines both require detailed audit trails of data access, modification, and transfer events, retained and available for regulatory review. On hyperscaler platforms, comprehensive audit logging is available but priced as a premium add-on. On IBEE, full audit logging is included as standard infrastructure, not an additional billing line.
The CERT-In 180-Day Log Retention Requirement
CERT-In's April 2022 mandatory directions require all organisations operating in India to maintain IT system logs for 180 days within Indian jurisdiction. For financial services companies, this creates an explicit requirement for India-resident log storage infrastructure. A hyperscaler's India region, operated by a US legal entity, does not straightforwardly satisfy "within Indian jurisdiction" as a legal matter.
The DPDP Act: Financial Data as Sensitive Personal Data
Under India's Digital Personal Data Protection Act 2023, financial information is classified as sensitive personal data, carrying heightened protection obligations. As data fiduciaries, banks, NBFCs, and fintech platforms are accountable for how this data is processed and where it flows. Using infrastructure governed by a foreign legal entity creates accountability ambiguity that the Act does not accommodate cleanly.
Latency in Real-Time Financial Transactions
Beyond compliance, there is a direct operational cost to hyperscaler latency in financial services. Credit decisioning engines, fraud detection systems, real-time payment processing, and trading infrastructure all have sub-100ms requirements. Generic hyperscaler infrastructure routed through shared global availability zones introduces latency that degrades system performance, particularly for customers in Tier 2 cities and for high-frequency transaction workflows.
How IBEE Solves the Financial Services Cloud Problem
IBEE Hosting operates from Tier 4 certified data centres in India, the highest internationally recognised tier for data centre reliability, delivering 99.995% uptime SLA. More importantly for financial services, IBEE is an Indian company, operating Indian infrastructure, governed by Indian law.
India-Sovereign Infrastructure: RBI, SEBI, IRDAI, and DPDP Aligned
Every byte stored with IBEE sits on infrastructure owned and operated by an Indian legal entity. There is no US CLOUD Act exposure. No foreign jurisdiction can compel data disclosure. No cross-border data access ambiguity.
What this gives financial services companies is something a US-headquartered cloud provider cannot offer: a clean, unambiguous chain of data custody under Indian law. That documentation is available for RBI inspection, SEBI audit, IRDAI compliance review, and DPDP Act accountability requirements, not as a configuration workaround, but as a baseline fact of the infrastructure.
We have seen this matter most acutely during banking partner due diligence. A payment platform using IBEE can respond to the jurisdiction question in one sentence. A platform on AWS Mumbai needs a legal memo. Auditors notice the difference.
Tier 4 Reliability: 99.995% Uptime for Mission-Critical Financial Systems
Payment platforms cannot go down during market hours. Loan origination systems cannot fail during peak application windows. Trading infrastructure cannot tolerate unplanned outages.
Tier 4 data centre certification means fully fault-tolerant infrastructure: dual power feeds, redundant cooling, zero single points of failure, and planned maintenance without downtime. For financial services, where every minute of downtime has a direct revenue and compliance consequence, the difference between Tier 4 and standard cloud SLAs represents approximately 26 fewer minutes of potential downtime per year.
CERT-In Compliant Audit Logging: Included as Standard
IBEE's audit logging infrastructure captures access records, API calls, object-level operations, and permission changes, maintained within India, on Indian infrastructure, under Indian jurisdiction. The 180-day retention requirement CERT-In mandates is met by default, not through additional configuration or additional cost.
Sub-5ms Latency for Indian Financial Workflows
IBEE's India-first infrastructure delivers sub-5ms object retrieval for Indian users. For real-time fraud detection engines reading transaction history, for credit bureau integrations pulling borrower records, for payment reconciliation systems processing high volumes at end-of-day, the difference between sub-5ms and the 15 to 40ms typical of hyperscaler India availability zones is measurable in production.
S3-Compatible API: Integrates with Existing Financial Technology Stacks
Core banking systems, loan origination platforms, insurance policy management systems, and trading infrastructure increasingly support S3-compatible object storage. IBEE's full S3 API compatibility means integration with existing financial technology stacks requires an endpoint change, not a re-architecture project.
Predictable Storage Costs for Long-Retention Financial Records
Financial records carry long mandatory retention periods: loan documents for 8 years, KYC records for 5 years after relationship closure, transaction records per RBI guidelines. IBEE's flat pricing model carries no retrieval surcharges and no archival tier penalties. Records accessed once a year for an audit cost exactly the same per-GB as records accessed daily.
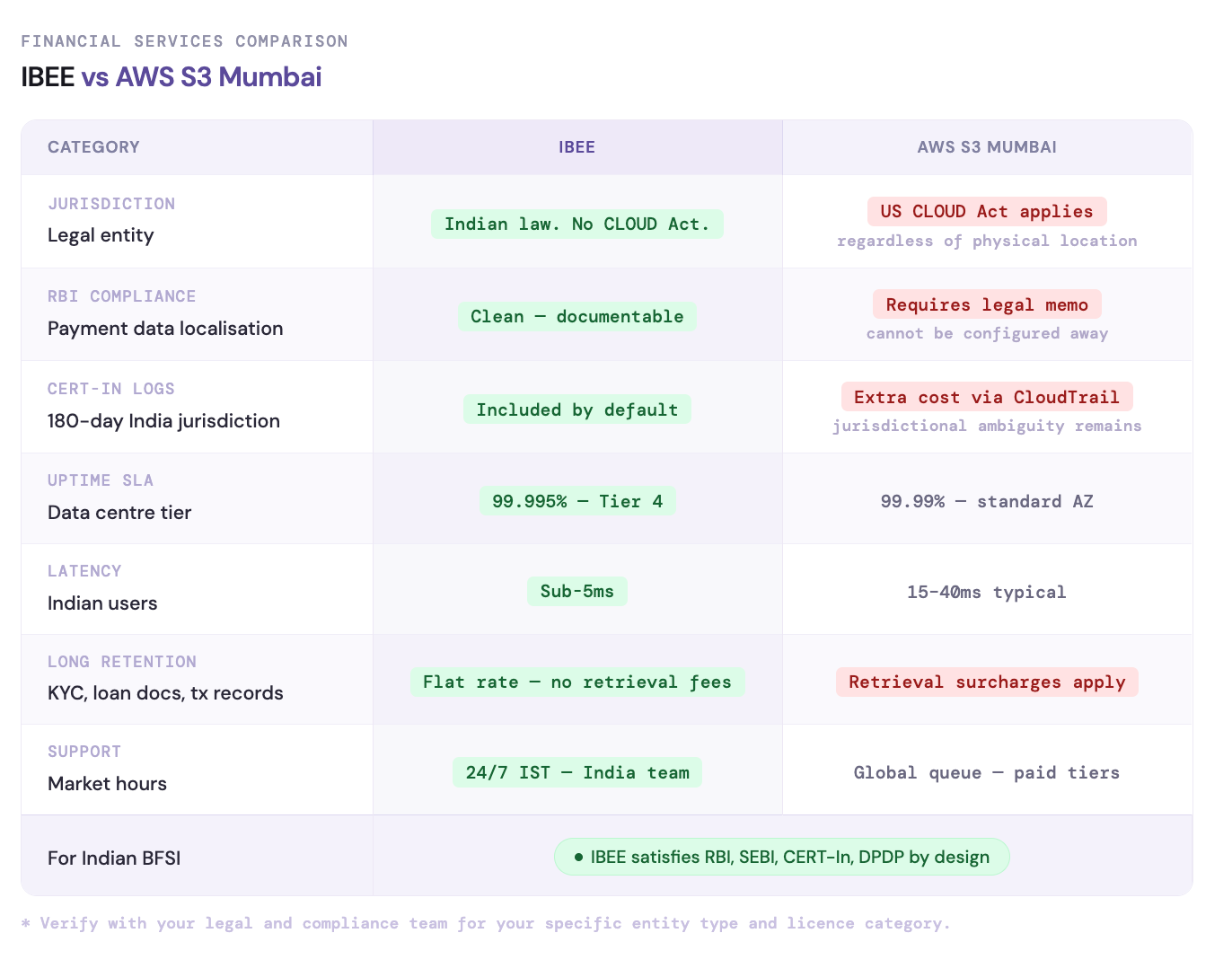
The compliance gap is the most consequential difference.
The Regulatory Framework IBEE Is Built to Satisfy
RBI Payment Data Localisation
The RBI's 2018 Storage of Payment System Data directive mandates that all payment data — transaction records, end-to-end details, customer financial information — be stored in systems located in India. IBEE's Indian-entity ownership and India-resident infrastructure provides the legal and physical basis for satisfying this directive cleanly.
SEBI Cybersecurity Framework
SEBI's cybersecurity and cyber resilience framework for market infrastructure institutions and registered intermediaries requires detailed IT audit trails, access controls, and data protection measures. IBEE's included audit logging, IAM-based access controls, AES-256 encryption, and Tier 4 reliability map directly to SEBI's framework requirements.
IRDAI IT and Cybersecurity Guidelines
IRDAI's guidelines for insurance companies require robust IT governance, data protection, and audit capabilities. India-sovereign infrastructure with documented compliance posture simplifies the annual IT audit process for insurance entities operating under IRDAI oversight.
CERT-In Mandatory Directions
CERT-In's April 2022 directions require all covered organisations to maintain logs within Indian jurisdiction for 180 days and report cybersecurity incidents within prescribed timelines. IBEE's audit infrastructure is built, operated, and retained entirely within India, satisfying the jurisdictional requirement without additional configuration.
DPDP Act 2023: Financial Data as Sensitive Personal Data
Financial information under the DPDP Act carries heightened protection obligations. Data fiduciaries — which includes virtually every financial services entity — are accountable for processing practices and data flows. IBEE's Indian-entity structure provides the clean accountability chain the Act requires.
The Compliance Clock Is Running
Indian financial regulators are not getting less demanding. The RBI's data localisation position has hardened over five years. SEBI's cybersecurity framework has been expanded. CERT-In's 2022 directions added new log retention obligations. The DPDP Act has added a legal accountability layer on top of all of it.
Every quarter a fintech, NBFC, or insurance company runs on hyperscaler infrastructure governed by US law, it accumulates compliance exposure that will eventually require resolution, either proactively through a planned migration, or reactively through a forced audit remediation that costs far more.
The infrastructure decision that financial services companies make now determines whether their next regulatory audit is a routine review or an expensive remediation project. We have seen both outcomes. The difference is almost always made two years earlier, when someone decided whether the cloud provider they were choosing was governed by Indian law or someone else's.
No credit card. No subscription. No minimum commitment.